Microchip Technology Inc. has announced four compact, low-power, highly integrated solutions that allow Wi-Fi and networking capability to be embedded into virtually any device, including Internet of Things (IoT) applications. These four modules provide complete solutions for 802.11b/g/n and are industry certified in multiple countries. The new RN1810 and RN1810E are stand-alone, surface-mount WiFly radio […]
IoT
Programming platform supports Python code execution directly IoT microcontrollers
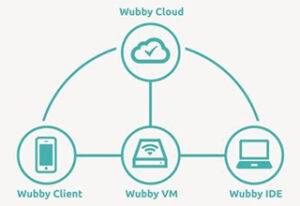
The new Wubby platform simplifies the development of IoT and Smart Home devices and systems by providing a programming environment that supports Python code execution directly in the microcontroller of the device. This allows a broader developer audience to create new everyday objects because of the popularity of Python. Wubby (pronounced Wha-bee) is the first […]
SoC supports low-power double-data-rate RAM for mobile apps
MediaTek today announced the MediaTek Helio P20 system-on-chip, an ultra-power saving SoC and the latest addition to its top-tier MediaTek Helio family of mobile processors. The MediaTek Helio P20 brings new experiences to consumers and design freedom to device makers by combining impressive battery life, powerful performance and premium features for the next generation of […]
HTML5-based OS targets mobile and IoT devices
ACADINE Technologies, an independent provider of operating systems software / service platforms for a new generation of smart devices, announced the release of H5OS, a scalable HTML5-based and commercially ready Operating System (OS) created for mobile devices and the IoT. H5OS’s design has two key products – H5OS CORE and H5OS Feature Packs – which […]
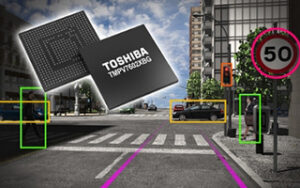
Image Recognition Processor handles Monocular Cameras In ADAS Apps
Toshiba America Electronic Components, Inc. (TAEC)*, has announced the newest addition to its TMPV760 family of image recognition processors for automotive applications. The TMPV7602XBG is suitable for monocular cameras used in Advanced Driver Assistance Systems (ADAS), and will help designers implement ADAS applications utilizing a cost-optimized camera system with a small form factor. The Toshiba […]
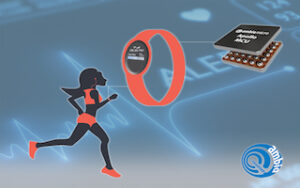
Ultra-low power Heart-Rate-Monitoring electronics for wearable products
Ambiq Micro and PixArt Imaging Inc. has announced that the two companies have partnered to develop an ultra-low power Heart-Rate-Monitoring (HRM) solution for deployment in next-generation wearable products. The fast-growing wearables market is rapidly evolving from devices that are primarily fitness-oriented to those that are intended to provide more sophisticated data and information on the […]
64-bitARM-Core LTE SoC platform targets 4G apps
Spreadtrum Communications (“Spreadtrum”), has announced its 64-bit Octa-Core LTE SoC platform, SC9860 chipset at mass production stage in 2016 Mobile World Congress (MWC) , Barcelona. As Spreadtrum’s single chip solution for medium and premium smart phones, SC9860 possesses excellent computing ability and features premium multi-media applications, which bring about ultimate user experience for global handset […]
SoC targets wearables with low-power processor, ultra-low power sensor hub
Qualcomm Incorporated today announced that its subsidiary, Qualcomm Technologies, Inc., has introduced Qualcomm Snapdragon Wear, a new platform for next generation wearable devices, and the Snapdragon Wear 2100 system-on-chip (SoC), the first in a new product family designed to bring new and enhanced wearable experiences to consumers. Utilizing Qualcomm Technologies’ expertise in connectivity and compute, […]
IoT framework software handles multi-protocol gateways, cloud management, gateway hardware and edge computing devices
eInfochips has announced its Internet-of-Things (IoT) framework called ‘IoT Xcelerator’, aimed at product companies that are looking to monetize opportunities in a hyper-connected future which would thrive on billions of smart devices. The IoT Xcelerator framework helps in reducing the time-to-market for clients who wish to develop IoT products and services across sensors, Cloud and […]
Modbus Protocol filter gives cyber attack protection for industrial automation & control systems
Icon Labs has announced the release of its Floodgate Modbus Protocol Filtering product. This extension to Icon Labs’ Floodgate Security Framework adds critical protection capabilities for Industrial IoT and RTOS-based devices. The Floodgate Modbus Protocol filter provides the critical missing layer of security for Modbus/TCP devices. Integrated into the device, Floodgate Modbus Protocol filtering utilizes […]