NXP Semiconductors announced the i.MX 91 applications processor family. Building on more than two decades of leadership in developing multi-market applications processors, the i.MX 91 family delivers an optimized blend of the security, features, and energy-efficient performance required for the next generation of Linux-based IoT and industrial applications. Emerging protocols such as Matter, the interoperable, […]
Security
AI-driven security processors integrate all security functions within single SoC or module
COMPUTEX 2023 Axiado Corporation introduced the AX3000 and AX2000 trusted control/compute units (TCUs), the world’s first fully integrated AI-driven hardware security platform solutions designed to help detect cybersecurity and ransomware attacks on next-generation servers and infrastructure elements in cloud datacenters, 5G networks, and network switches. Samples of AX3000/AX2000 TCUs are available now. Axiado’s TCU comes […]
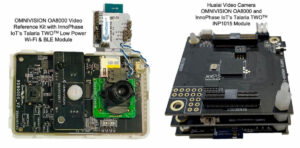
Wi-Fi, Bluetooth module cuts power consumption in video IoT devices
InnoPhase IoT, Inc. unveiled its Talaria TWO Ultra-low power (ULP) Wi-Fi optimized market-ready solutions for cloud-connected IP video IoT devices. Applications include battery-operated video cameras, smart video doorbells, wearables, smart appliances, home security cameras, and in-vehicle dashboard monitoring devices. Talaria TWO features for video use-cases include: Integrated Wi-Fi and Bluetooth Low Energy (BLE) for easy […]
Hybrid cloud + edge platform helps bring voicechat capabilities to consumer devices
Sensory has announced a breakthrough technology integration that enables ChatGPT or other Large Language Models to drive conversational voice responses (VoiceChat) on consumer products and other devices lacking keyboards and big screens. Targeting in-ear voice assistants, smartwatches, smartphones, automotive infotainment systems, and more, this powerful technology integration delivers a fast and seamless conversational experience on […]
Zigbee protocol stack revision includes additional security enhancements
The Connectivity Standards Alliance announced the release of Zigbee PRO 2023 of the Zigbee protocol stack. The revision brings several enhancements and new features to the technology, allowing mesh networks to have a universal language that enables smart objects to work together. Zigbee PRO 2023 expands on secure-by-design architecture by adding a number of security enhancements […]
IoT controller brings wired and wireless computing to the edge
ASRock Industrial is excited to release the iEP-7020E Series Industrial IoT Controller enabled by 13th Gen Intel Core Embedded and Industrial Processors (Raptor Lake-P) for optimized performance and scalability. Intel Iris Xe graphics for fast AI and Intel In-Band ECC support, delivering intelligent and reliable control over vital processes at the edge. The iEP-7020E Series […]
SOM provides complete and scalable platform for IoT edge devices
Arduino announces the launch of its new Portenta C33 System-on-Module (SOM), based on the RA6M5, an Arm Cortex M33-based microcontroller from Renesas. Portenta C33 is the latest addition to Arduino’s Portenta family, which is specifically designed to provide a complete and scalable platform for IoT edge devices. Portenta C33 offers a powerful microcontroller, connectivity, and […]
Connected MCU helps deliver faster, more secure NFC authentication
NXP Semiconductors has announced the PN7642, a single-chip solution that integrates a customizable MCU, an NFC reader, and SESIP-Level 2 security to help deliver faster, more secure NFC transactions for physical access solutions, consumables authentication, secure identity verification, and other NFC use cases. NFC technology has become foundational to secure authentication, whether it’s verifying that […]
Processors targeted for heavy-workload, always-on embedded systems
AMD announced it is bringing world-class performance and energy efficiency to embedded systems with AMD EPYC Embedded 9004 Series processors. The new 4th generation EPYC Embedded processors powered by “Zen 4” architecture provides technology and features for embedded networking, security/firewall, and storage systems in cloud and enterprise computing as well as industrial edge servers for the factory floor. […]
Six security-focused devices aim to optimize and scale embedded security
Embedded security continues to be a high priority, and architects need vetted easy-to-use, and cost-optimized security solutions that are compliant with industry best practices. To provide architects with comprehensive embedded security solutions, Microchip Technology announces it has expanded its secure authentication device portfolio with six new products in its CryptoAuthentication and CryptoAutomotive IC families that meet Common Criteria Joint Interpretation […]