Synopsys announced the new Enhanced Security Package for Synopsys DesignWare ARC HS Processors, enabling designers to develop isolated, secure environments that help protect embedded systems and software from evolving threats in high-end automotive, storage, and gateway applications. The Enhanced Security Package incorporates a range of features, including integrity protection, multiple privilege levels, and a watchdog timer that […]
Security
Secure bootloader leverages cryptography module to provide signature authentication
wolfSSL announces the commercial release of wolfBoot! wolfBoot is a secure bootloader that leverages wolfSSL’s underlying wolfCrypt module to provide signature authentication for the firmware. The role of a secure bootloader is to effectively prevent the loading of malicious or unauthorized firmware on the target. Additionally, wolfBoot provides a fail-safe update mechanism that can be […]
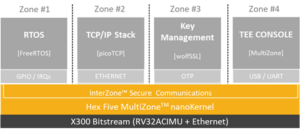
First secure IoT stack for RISC-V enables unlimited number of secure zones
wolfSSL and Hex Five Security, provider of MultiZone Security, the first Trusted Execution Environment for RISC-V, announce general availability of the industry-first secure IoT stack for RISC-V – a TLS 1.3 reference implementation of freeRTOS with hardware-enforced separation between OS, TCP/IP stack and root of trust. FreeRTOS is the leading real-time operating system in the market; […]
Radix-S hardware-based security system IDs system-level vulnerabilities
Tortuga Logic, a cybersecurity company specializing in hardware threat detection and mitigation, today announced the release of Radix-S, the first product in a series of hardware-based security solutions designed to identify system-level vulnerabilities embedded in Hardware Roots of Trust (HRoT). A Hardware Root of Trust is a minimum set of hardware and software that is trusted to […]
Cybersecurity basics: Authentication and “key” management in LoRaWAN, Part 2
In part 1, we described the process of providing end-to-end security and some of the challenges in achieving network security. In this installment, we will go over how authentication work to achieve end-to-end network security between the end devices and the application servers. Device authentication and key management Each LoRaWAN device is given a unique 128-bit […]
Secure provisioning service builds-in security from inception to life of LoRaWAN device
Just as agile software principles are being adapted for hardware development, so secure provisioning IT practices are finding their way into the semiconductor industry — a move accelerated by the necessity of keeping the increasing number and vulnerability of connected IoT devices. While LoRa technology is sweet spot for low-power connectivity, security remains an area for […]
Static analysis technology updated with security for enterprise applications
Synopsys, Inc. announced the availability of a new version of its Coverity static application security testing (SAST) solution, which enables organizations to build secure applications faster. The latest release of Coverity addresses three increasingly important needs for enterprise application security teams: scalability, broad language and framework support, and comprehensive vulnerability analysis. Coverity enables enterprise organizations to scale […]
BGP hijacking: How the Internet is getting hacked and what you can do about it
By Rudy Ramos, Mouser Electronics Most of us are familiar with the tricks used by malicious hackers to steal passwords or intercept private data. When we click a link, or start a chat, or send an email, it’s second nature to quickly check URLs and addresses to make sure that our data is going where […]
SoCs enable secure intelligence at the edge
Synaptics Incorporated announced its new AS3xx series, a comprehensive family of Smart Edge AudioSmart solutions including the world’s first fully integrated SoCs comprising neural network acceleration, a proprietary wake word engine with support for custom wake words, and highly-advanced far-field voice processing. Designed using a 22nm process node, and targeting a broad variety of voice-enabled Smart Home […]
IoT framework helps secure sensors and gateways
Dublin-based secure hardware and software technology developer Firmwave today announced the availability of new IoT EST and validation services to help make sensors and gateways more secure. “There are many potential points of failure in an end-to-end IoT Solution, and the world of connected products is full of examples of bad security,” said Mike Hibbett, […]