The microcontroller, the most widely deployed computing platform, is ready to welcome the artificial intelligence (AI) revolution. Really? For a start, MCUs don’t have enough storage space needed to hold the neural network-based trained models, and they don’t have enough RAM to carry out inference operations based on these models. Microcontrollers are known for limited […]
Featured
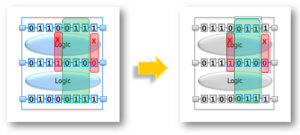
A new technique to maximize scan diagnosis throughput
by Jayant D’Souza, product manager Tessent group at Mentor, a Siemens Business Charged with the task of improving yield, product engineers need to find the location of defects in manufactured ICs quickly and efficiently. Typically, they use failing test cycles to perform scan diagnosis, which is then analyzed to reveal the location and root cause […]
How to make the most of low-cost satellites for remote IoT apps
It’s now cheaper than ever to launch small and nano-satellites into space thanks to NASA’s CubeSat Launch initiative (CSLI) – and this is excellent news for developers of remote Internet of Things (IoT) applications. For the uninitiated, CubeSats are research spacecraft that measure around 4 inches (102mm) long and are taken into space on rocket […]
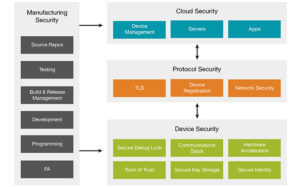
Cloud connectivity in IoT, Part 2: How to secure data links
If the Internet of Things (IoT) is about connecting objects like a thermostat or a pacemaker to the Internet Protocol (IP)-based networks, then it’s even more about securing links to these objects. And that includes implementing security while connecting IoT devices to a cloud platform. The good news is that securing links to the cloud […]
Cloud connectivity in IoT, Part 1: How communication works
Cloud connectivity, a fundamental part of the majority of the Internet of Things (IoT) projects, is intertwined with expertise in embedded systems and software integration. That’s why MCU suppliers are working closely with cloud service providers to develop integrated hardware and software solutions that enable IoT developers to establish an edge-to-cloud connection using out-of-the-box solutions […]
Embedded basics Part 3: Functional safety documentation and terminology
Functional safety compliance is often a time-consuming and expensive process. That, in turn, underscores the role of documentation in efficiently implementing the functional safety guidelines. So, designers need full documentation to support the development of functional safety-enabled embedded systems. It includes safety manuals that document all the information for integrating functional safety-enabled MCUs into the […]
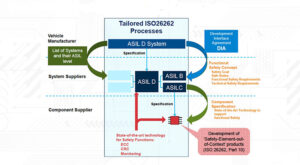
Embedded basics Part 2: ISO 26262 functional safety for MCUs
Functional safety, a critical requirement in automotive applications, addresses catastrophic failures from data corruption by attaining Automotive Safety Integrity Levels (ASILs) as per ISO 26262 standard. Contrary to the common perception that only large and powerful system-on-chips (SoCs) incorporate functional safety built around the ISO 26262 standard, MCUs for the next-generation car architectures are increasingly […]
Where is embedded security headed in the IoT?
By Alex Koepsel, IoT Marketing Manager, Silicon Labs If you consider how much digital security has evolved in recent years, it is quite astonishing. Our mindset and social acceptance of what is “secure” has changed dramatically over time. For example, before the adoption of ATMs for personal cash withdrawals, the only place you trusted to […]
Embedded basics Part 1: IEC 61508 functional safety for MCUs
Functional safety is becoming one of the most important features in embedded systems, especially in the automotive and industrial markets, where safety and reliability are critical design attributes. It encompasses the development of a Safety Integrity Level (SIL) according to IEC 61508 functional safety standard for the general industry and an Automotive Safety Integrity Level […]
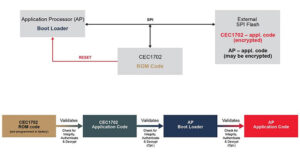
Four major design considerations for IoT apps secure boot
Secure boot, the first line of defense against security breaches in embedded systems, verifies the pre-boot authentication of system firmware using a root-of-trust service and thus safeguards code and data to prevent malicious activities. It’s a critical security measure to protect connected devices like the Internet of Things (IoT) endpoints because most security breaches such […]