Single-Pair Ethernet (SPE) is defined in IEEE 802.3 and adapts the basic Ethernet standard to use a single wire pair. Power over data line (PoDL) is sometimes referred to as power over Ethernet (PoE) adapted for SPE. That’s only partially correct, PoDL is optimized specifically for use in automotive and similar environments, and the newer […]
Featured
Chipset, network, module partnership brings LTE connectivity to IoT devices
Engineers designing IoT devices need to focus on the hardware and software for their device’s applications such as smart meters, logistics tracking devices, and so on. For many designers, connectivity is not their area of expertise. Soracom, a provider and SIM cards and eSIM devices for IoT, has partnered with Sony Semiconductor (formerly Altair) and […]
August 2023 Issue: Automotive & Transportation Electronics
In this issue Smarter, safer, cheaper: how Ethernet will enable the car of the future The implementation of Ethernet as a universal standard throughout the automotive industry can optimize vehicle performance by reducing the number of electronic control units (ECUs) and associated wiring, thus enabling a smarter, cheaper, and safer future car. Zonal E/E will…
How do MCUs support automotive infotainment systems?
In vehicle infotainment (IVI) systems are increasingly important and complex. What’s needed from a microcontroller (MCU) in an IVI? A lot, but exactly what depends on the sophistication and mix of info and ‘tainment. Multiple cores are often needed, and so are hardware accelerators for compute-intensive functions. Considerations include connectivity, human-machine interfaces (HMIs) beyond simple […]
Key factors to optimize power consumption in an embedded device
In the previous article, we learned what a low-power system is, so now we’ll talk about the key factors which can make a power-efficient embedded system design. The power-efficient embedded system is comprised of hardware and software design along with proper components selection. Optimization is achieved by efficient implementation in different stages using different techniques. […]
How to optimize Arduino for low power design
Power consumption of the embedded controller is a primary concern in low-power design. Arduino boards are often used in devices that rely on battery or solar charging. Such devices often deploy far from the power line to have periodic battery replacement or are mobile devices designed for periodic charging cycles. In such a case, optimizing […]
How do the seven types of V2X connectivity work?
Vehicle-to-everything (V2X) communication includes vehicle-to-network (V2N), vehicle-to-infrastructure (V2I), vehicle-to-vehicle (V2V), vehicle-to-cloud (V2C), vehicle-to-pedestrian (V2P), vehicle to device (V2D), and vehicle to grid (V2G). This FAQ begins with a review of dedicated short-range communication (DSRC) and cellular vehicle-to-everything (C-V2X) technologies for V2X communications, looks at the four V2X service types and the structure of telematics control […]
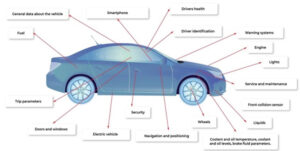
What are the five levels of vehicle connectivity?
There are several efforts underway to define levels of vehicle connectivity that parallel the levels of driving automation defined by the Society of Automotive Engineers (SAE). The concept of autonomous vehicles, particularly at the higher levels of automation like self-driving cars, is still largely aspirational and a goal for some time in the future. Connectivity, […]
What’s different about MCUs for use in vehicle networking?
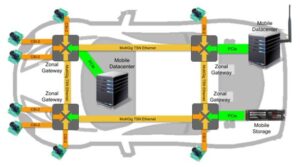
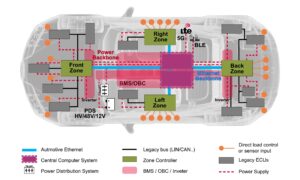
The increasing use of automated driving functions, more sensors and actuators, and growing V2X connectivity is increasing the challenges related to vehicle electric/electronic (E/E) architectures and in-vehicle networking (IVN). This FAQ will review the performance requirements for microcontrollers (MCUs) needed to support time-sensitive networking (TSN) in IVNs, move over to look at service-oriented gateways, domain […]
Zonal E/E will transform automotive architectures
The transition from numerous ECUs to zones will occur over several years from roughly 2025 to 2030. Each OEM will use its own architecture. Long before the smartphone, the number of interconnected electronics and electrical equipment on automobiles, especially high-end vehicles, led pundits to describe a car as a computer on wheels or a digital […]