A report from the NASA Office of Inspector General released a few days ago reveals the network within NASA’s Jet Propulsion Lab was compromised in a manner resembling that portrayed in an episode of the popular TV series, Mr. Robot.
In April 2018, JPL discovered an account belonging to an external user used to log into JPL’s
mission network had been compromised. Because of how JPL’s network is architected, the attackers were able to expand their access upon entry and move laterally across the network. The attack went undetected for nearly a year.
One reason the attack was successful, says the report, is that NASA system administrators often don’t regularly enter new devices into an information technology security database (ITSDB) because the database’s updating function sometimes doesn’t work. So items can be added to the network without being properly identified and vetted. The report says the April 2018 cyberattack exploited this particular weakness when the hacker accessed the JPL network by targeting a Raspberry Pi connected to the network that wasn’t authorized to be there.
The report seems to imply that the Raspberry Pi had been added innocently but ended up being a 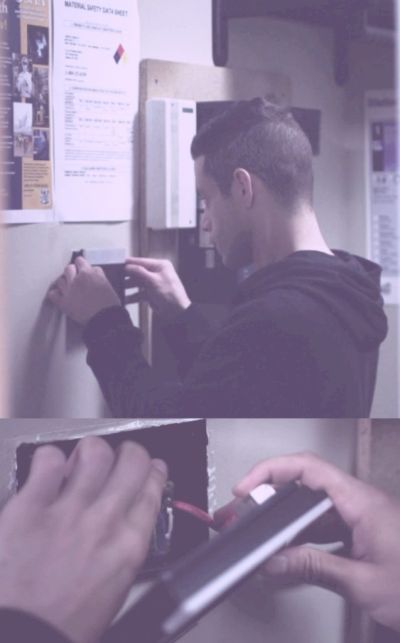
Once the Raspberry Pi had been added to the HVAC network, the Mr. Robot hackers accessed it remotely via a real-life website called Shodan (www.shodan.io), a search engine that lets users find not just HVAC systems but also routers, servers, and other equipment connected to the internet. The hack on TV worked because the building HVAC network was connected directly to the internet (a practice that security professionals warn against) and because the HVAC network had no means of authenticating devices connected to it. (Security professionals say this security defect is common among older industrial network standards.)
An additional common factor between the Mr. Robot hack and the NASA infiltration seems to be a lack of visibility for network connections. According to the NASA report, the attacker, using an external user account, exploited weaknesses in JPL’s system of security controls to move undetected 
The NASA report also said the cyberattacker from the April 2018 incident exploited the JPL network’s lack of segmentation to move between various systems connected to a network gateway, including multiple JPL mission operations and the deep space network.
NASA says it has since installed additional safeguards on its firewalls and has implemented other security measures.




Leave a Reply