TDK Corporation announced the launch of its new M.2 2280 type SSD [SNP1A series], supporting PCI Express (PCIe)* and NVM Express (NVMe)**. The SSD integrates NAND flash memory, TDK’s GBDriver GX1 controller IC, and an internal backup power circuit, making it highly resistant to power interruptions. In recent years, the number of SATA ports on […]
Security
Low-power devices address IoT applications
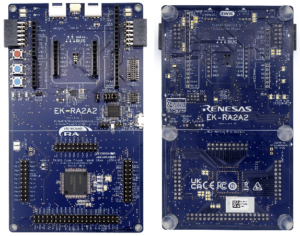
Renesas Electronics Corporation has launched the RA2A2 microcontroller (MCU) Group powered by the Arm Cortex-M23 processor. These new low-power devices feature a 24-bit Sigma-Delta analog-to-digital converter (SDADC) and an innovative dual-bank code flash with a bank swap function, facilitating firmware over-the-air (FOTA) updates for smart energy management, building automation, medical devices, consumer electronics, and other […]
Root-of-trust devices accelerate secure manufacturing and deployment
Microchip Technology is helping make embedded security solutions more accessible with its CEC1736 TrustFLEX devices. The CEC1736 Trust Shield family is a microcontroller-based platform root of trust solution enabling cyber resiliency for data centers, telecom, networking, embedded computing, and industrial applications. Now, as part of the TrustFLEX platform, the devices are partially configured and provisioned with Microchip-signed […]
Automotive SoC offers advanced security and communications for vehicle interfaces
Infineon Technologies AG has launched the new Automotive PSoC 4100S Max family. This microcontroller device family expands Infineon’s portfolio of CAPSENSE-enabled Human Machine Interface (HMI) solutions for automotive body/HVAC and steering wheel applications by delivering higher flash densities, GPIOs, CAN-FD, and HW-Security. The Automotive PSoC 4100S Max with fifth-generation CAPSENSE technology offering 10x higher sensitivity […]
Wireless SoC features low power consumption and enhanced security features
Sony Semiconductor Israel announced that its advanced ALT1350 Wireless System on Chip (SoC) is now commercially available. LPWA cellular modules have been designed by our partners and industry leaders AM Telecom, Fibocom, Murata, Quectel, Semtech, Telit Cinterion, and Wistron NeWeb Corporation (WNC). The modules are now available for sampling, with mass production expected during the […]
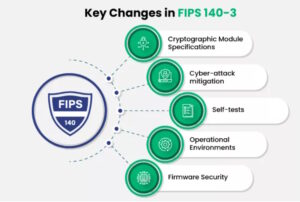
Securing devices for the IoT – FIPS 140-3 and common criteria
For developers of IoT devices and networks, the Federal Information Processing Standard (FIPS) 140-3 and the Common Criteria (CC) serve different but complementary functions. FIPS 140-3 is designed for validating software and hardware in cryptographic modules, while CC is designed to evaluate security functions in IT software and hardware. In both cases, there are related […]
Securing devices for the IoT — IEC 62443, SESIP, and PSA
The International Electrotechnical Commission (IEC) 62443 series of standards is focused on security for Industrial Automation and Control Systems (IACS); the Security Evaluation Standard for IoT Platforms (SESIP) provides a method for trustworthy assessment of the security IoT platforms, including the industrial IoT (IIoT), and Platform Security Architecture (PSA) certification requires strict adherence to the […]
Securing devices for the IoT – managing memory
Memory management is important in all digital electronic devices including devices designed for use on the Internet of Things (IoT). It supports efficient resource allocation and memory utilization and prevents memory fragmentation, improving efficiency. It also supports memory protection and device security. This FAQ briefly reviews the common weakness enumeration (CWE) scheme for identifying software […]
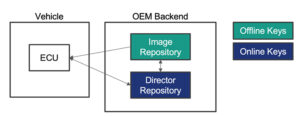
Securing devices for the IoT – firmware, software, and OTA
Over-the-air (OTA) updating of firmware and software on Internet of Things (IoT) devices is a requirement, not an option. The large number of IoT devices makes manual updates impractical and even dangerous. This FAQ reviews two key tools for managing and implementing OTA for IoT devices: open-source standards for managing resource-constrained devices and industry standards […]
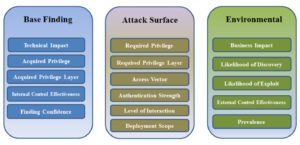
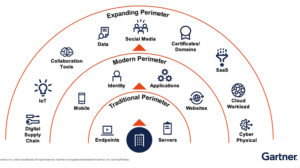
Securing devices for the IoT — minimize the attack surface
An attack surface is the sum of all the attack vectors or ways that an attacker can gain malicious access to a network or system. The growth in remote work and the adoption of cloud services have increased the number of attack vectors and the size of the attack surface for most organizations and applications. […]