Synopsys, Inc. announced the availability of a new version of its Coverity static application security testing (SAST) solution, which enables organizations to build secure applications faster. The latest release of Coverity addresses three increasingly important needs for enterprise application security teams: scalability, broad language and framework support, and comprehensive vulnerability analysis. Coverity enables enterprise organizations to scale […]
Security
BGP hijacking: How the Internet is getting hacked and what you can do about it
By Rudy Ramos, Mouser Electronics Most of us are familiar with the tricks used by malicious hackers to steal passwords or intercept private data. When we click a link, or start a chat, or send an email, it’s second nature to quickly check URLs and addresses to make sure that our data is going where […]
SoCs enable secure intelligence at the edge
Synaptics Incorporated announced its new AS3xx series, a comprehensive family of Smart Edge AudioSmart solutions including the world’s first fully integrated SoCs comprising neural network acceleration, a proprietary wake word engine with support for custom wake words, and highly-advanced far-field voice processing. Designed using a 22nm process node, and targeting a broad variety of voice-enabled Smart Home […]
IoT framework helps secure sensors and gateways
Dublin-based secure hardware and software technology developer Firmwave today announced the availability of new IoT EST and validation services to help make sensors and gateways more secure. “There are many potential points of failure in an end-to-end IoT Solution, and the world of connected products is full of examples of bad security,” said Mike Hibbett, […]
32-bit MCUs qualified with Amazon FreeRTOS on AWS
Renesas Electronics Corporation announced the qualification of their RX65N Group of microcontrollers (MCU) with Amazon FreeRTOS, running on Amazon Web Services (AWS). The Renesas RX65N MCU lineup with Amazon FreeRTOS makes it easy for embedded designers to create a more secure end-to-end Internet of Things (IoT) cloud solution for sensor-based endpoint devices. An RX65N-based design […]
Better security for automotive 8-port Ethernet gigabit capacity switch
Argus Cyber Security and Marvell announced today that the Argus IDPS Ethernet solution will be integrated into Marvell’s highly secure 88Q5050 automotive Ethernet switch. The integration of the Argus solution will provide Marvell’s 8-port Ethernet gigabit capacity switch with an enhanced level of security. The solution empowers OEMs to deploy advanced Ethernet capabilities with the ability to prevent and […]
Embedded board offers POE, multi-size display support
The new EMB-7610 from Estone Technology is a proprietary form factor board, 160mm x 90mm, designed especially for digital surveillance, in-vehicle electronics, industrial automation, retail and medical technologies. Available Power Over Ethernet and Estone Tech’s proprietary 40-pin expansion header open up plenty of additional uses. The fanless design is industrial rugged, and will operate in temperatures […]
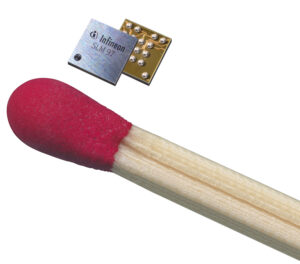
16- and 32-bit security eSIM controllers optimized for M2M
Machine-to-machine communication in the Internet of Things (IoT) requires reliable data collection and uninterrupted data transmission. For taking full advantage of the ubiquitous mobile networks, Infineon Technologies AG provides the world’s first industrial-grade embedded SIM (eSIM) in a miniature Wafer-level Chip-scale Package (WLCSP). Manufacturers of industrial machines and equipment ranging from vending machines to remote […]
Multi-format video encoder IP for 4K/UHD video
Allegro DVT announced the availability of AL-E200, a new generation of video encoder IPs built around a higher performance architecture and featuring many new optional smart encoding features. The AL-E200 encoder IP implements an enhanced single-core hardware architecture that enables encoding of UHD/4K resolutions. Furthermore, it provides support for multiple video codec formats by sharing resources […]
IoT platform libraries now comply with FIPS 140-2 cryptographic standards
Express Logic has partnered with one of the world’s leading security labs atsec information security to execute the design and implementation of the X-Ware IoT Platform’s NetX Crypto libraries for compliance with Federal Information Processing Standards (FIPS) 140-2 cryptographic standards. The certification authority for this effort, the National Institute of Standards and Technology (NIST), issued the […]