A few best practices can drastically improve the security of IoT devices and help maximize the benefits they provide.
CHRISTOPHE TREMLET,
SCOTT JONES
MAXIM INTEGRATED
 The news back in March was certainly alarming – WikiLeaks announced it had internal CIA documents revealing that the spy agency had found a way to access Android and Apple smartphones, Samsung smart TVs, and internet-enabled cars. The leak named dozens of device-specific vulnerabilities and attacks.
The news back in March was certainly alarming – WikiLeaks announced it had internal CIA documents revealing that the spy agency had found a way to access Android and Apple smartphones, Samsung smart TVs, and internet-enabled cars. The leak named dozens of device-specific vulnerabilities and attacks.
A regular string of headlines brings stories about the hacking of seemingly innocuous items like baby monitors, home security cameras, and even dolls. The scary part is, entry into these types of devices can potentially open avenues into the larger enterprise network. From here, scenarios such as spying, physical break-ins, identity theft, malware injection, and further attacks can become reality.
Unfortunately, the smarter and more connected our devices, the more vulnerable they can be to hackers. Scripts and bots are on the hunt, randomly scanning ports for opportunities to attack. Products themselves are often developed with plenty of entry points and little in the way of security. For example, proprietary RF technology may lack authentication or encryption. Sometimes, the issue is on the part of the end user employing default passwords and usernames, not updating apps, or using weak passwords on vulnerable devices such as routers.
There are more than six billion connected devices in use globally, expected to hit 20 billion by 2020. So the stakes certainly are high—for both hackers and their victims. ForeScout’s IoT Enterprise Risk Report1, developed with research by ethical hacker Samy Kamkar, identified seven internet of things (IoT) devices that can be hacked in just three minutes:
IP-connected security systems
IP-connected infrastructure such as climate control and energy meters
Smart video conferencing systems
Connected printers
Voice-over-IP phones
Smart refrigerators
Smart light bulbs
The report says hackers who gain access to these devices can plant backdoors that let them launch automated IoT botnet distributed denial-of-service (DDoS) attacks. For example, with smart enterprise security systems, the threat is that cybercriminals could use jamming or spoofing techniques to gain control over motion sensors, locks, and surveillance equipment. Configuration settings of VoIP phones can be exploited to evade authentication—and unveil opportunities to listen in on and record calls. And the breaching of connected HVAC systems and energy meters could let criminals manipulate them to, for instance, overheat critical infrastructure.
For those on the wrong side of the law, pursuing an attack often comes down to a risk-versus-reward game. So it’s up to their opponents—including design engineers—to build-in security early in a design. Often, though, design security is an afterthought because of the perceived cost and time involved in implementing it. Addressing security when it’s too late comes with drawbacks, too, as a “band-aid” approach doesn’t necessarily seal all potential points of entry.
A completely unbreakable security system isn’t realistic, but it is feasible to design products that incorporate state-of-the-art cryptographic protection that can only be hacked with a large investment in both money and time. A connected product must be infused with security from the sensor to the cloud. It’s important to verify all connections and interfaces, comply with appropriate standards, and root out possible issues via quality assurance testing. For example, implementing secure boot helps ensure that an electronic device only operates when it executes authenticated (trusted) software. A secure IC with dedicated functionality can help accomplish this level of security, and more.
It is critical to deploy technology that provides an authenticated data chain, from a protected sensor node to the web server. Also important is the strong protection of the IoT device via a secure microcontroller, for example, one that provides a secure boot and can establish secure communication between the host system and device.
Secure authentication is essential, offering the assurance that an IoT device and any endpoints are genuine, trusted, and safe. Also important is ensuring that the information either consumed or produced by the device has cryptographic integrity.
There are different methods for implementing authentication. They range from password-based, which is weak, to the stronger cryptographic digital signature method. This latter method comes in two different flavors of algorithms: symmetric and asymmetric. We’ll take a closer look at each approach.
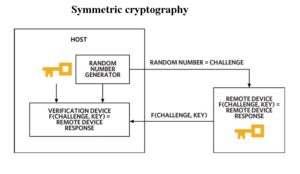
Symmetric cryptography-based authentication utilizes a shared secret key between the host and the device to be authenticated. This shared key is securely stored in both locations and never disclosed. The host sends a random number, the challenge, to the device. The device then computes a digital signature as a function of the secret and the challenge, sending it back to the host.
Next, the host runs the same computation and compares the result. The device is considered authentic if both computations match. Similarly, the host could request information from the device by sending a command with a random challenge. The device would generate the information — for example an environmental measurement — and compute a digital signature with the secret, challenge, and measurement, sending the signature and measurement back to the host. For this example, the host can verify the measurement has not been modified and comes from an authentic device.
It is critical to use a function with adequate mathematical properties to ensure the result can’t be mimicked, known as a replay attack. SHA-256 and similar secure hash functions meet this need. In fact, because SHA-256 is non-reversible, it is computationally infeasible to determine the input, which includes the secret, corresponding to a message authentication code (MAC). They’re collision-resistant as well, making it impractical to find more than one input message producing a given MAC.
These characteristics make SHA-256 highly effective for secure authentication. For a comparable security level, symmetric key authentication offers less algorithm complexity and shorter computation time than another approach called asymmetric cryptography. However, the shared key requirement results in a key distribution challenge.
ASYMMETRIC CRYPTOGRAPHY
Asymmetric cryptography-based authentication uses a mathematically linked key pair, a private key and public key. Only the device that needs to be authenticated knows the private key. The public key, on the other hand, can be shared with any entity with a requirement to authenticate the device.
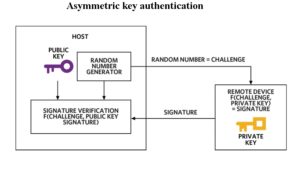
As with symmetric cryptography, the host sends a challenge to the device. The device then computes a signature based on the challenge and the private key, sending it back to the host. In this method, the host uses the public key to verify the signature.
Also, as in the previous example, information consumed or produced by the device can be authenticated within this asymmetric structure. Again, the function used to compute the signature must have certain mathematic properties to prevent replay attempts and key disclosure.
An efficient solution for embedded environments is the asymmetric Elliptic Curve Digital Signature Algorithm (ECDSA). It provides strong security for systems where it’s hard or even impossible to secure host keys. As compared to the symmetric approach, asymmetric key authentication has a more complex algorithm and longer computation time for a comparable security level. However, key distribution is efficient given there’s no security risk in openly transmitting a public key.
Secure microcontrollers and authenticators, such as those offered by Maxim’s DeepCover portfolio, integrate advanced hardware-based cryptography with physical security to provide strong protection against tampering and reverse engineering. In the portfolio are microcontroller and authenticator products that support both symmetric and asymmetric cryptography for digital signature, authentication, and encryption algorithms.
The devices selectively have hardware accelerators for SHA, RSA, ECDSA, and AES, a full cryptography library with a turnkey API aligned to standards, and built-in secure boot capabilities to guarantee firmware or file download authenticity. One example is the DeepCover cryptographic controller for embedded devices, the MAXQ1061. A turnkey pre-programmed secure microcontroller, the MAXQ1061 offers secure key storage, digital signature, and encryption services.
To shorten design time and accelerate time to market, Maxim provides an evaluation kit that can plug directly into a Raspberry Pi board. A comprehensive set of software libraries including a full TLS stack makes it a turnkey solution.
Reference designs provide another way to design for security early on and efficiently. Today’s high-quality reference designs are highly integrated and thoroughly vetted. Providing much more than just hardware and source software, good reference designs now commonly include Gerber files, test data, a detailed bill of materials (BOM), drivers, and evaluation and development tools.
For example, Maxim’s MAXREFDES155# IoT embedded security reference design provides a means to implement ECDSA public-key asymmetric cryptography to protect IoT devices and data paths. Optionally, the MAXREFDES143# protects devices and data paths with SHA-256 secret-key cryptography. Use of these reference designs can help simplify the process of developing devices that can authenticate and manage a sensing node with control and notification from a web server or a network controller.
The task of designing security for an IoT design needn’t be onerous, nor must it be costly. Developers just need to ensure the amount of security tips the risk-versus-reward balance. A system that is too difficult, expensive, and/or time-consuming to hack could turn the attention of cybercriminals toward other devices with more lax security.
Furthermore, technologies like secure microcontrollers and authenticators, along with fully integrated reference designs, make it faster and easier to guard designs against the prying intentions of hackers. Design safeguarding can go a long way in protecting reputations, customer experiences, networks, and, ultimately, bottom lines.
RESOURCES
ForeScout IoT Enterprise Risk Report, Forescout.com/wp-content/uploads/2016/10/iot-enterprise-risk-report.pdf
Maxim Integrated, www.maximintegrated.com/
Leave a Reply