In this context, a “fabric” is a group of networked devices that share the same security domain enabling secure communications within the fabric. Devices in each fabric share the same top-level certificate authority (CA), a Root of Trust determined by the CA, and have a unique (usually 64-bit) identifier called the Fabric ID. To add […]
FAQ
What’s a distributed compliance ledger and how is one integrated into Matter?
A distributed ledger is a type of database that’s shared, copied, and synchronized within a decentralized network. The general principal is similar to the blockchain technology used by cryptocurrencies like Bitcoin. The distributed compliance ledger (DCL) developed by the Connectivity Standards Alliance (CSA), developers of Matter, is a type of distributed ledger used during the […]
What are the top programming languages for machine learning?
Artificial intelligence (AI) and machine learning (ML) are continuing to become more mainstream and you’ll find the technology in everything from your smartphone apps and computer programs to smart tech and appliances — and automobiles (think self-driving cars). These technologies are no longer confined to scientific computing and statistical research but have, for the most part, become a […]
What can designers make with Matter?
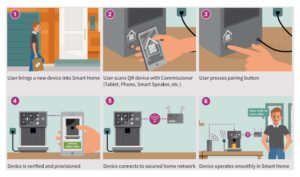
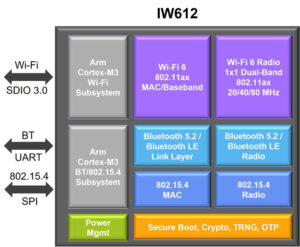
Matter enables designers to develop smart home accessories that work across all major wireless platforms. Mesh functions are possible because Matter operates as an application layer on top of technologies like Ethernet, Wi-Fi, Bluetooth, and Thread. Matter aims to simplify the setup and use of compatible smart home devices and bring some level of interoperability […]
What are the constituents of Matter?
Not elementary particles. The Matter being discussed here is an interoperable application layer software suite for wireless IoT devices. The constituents of that Matter include a modular software stack plus bridges, controllers, border routers, security including authentication, and cloud connectivity. Matter uses Thread, Wi-Fi, Ethernet transport, and Bluetooth LE for commissioning. Matter was initially called […]
How does Matter work as middleware for IoT devices?
Matter has been called an interoperable application layer solution, and the same source, the Connectivity Standards Alliance that oversees the development of Matter, refers to it as a protocol. This FAQ explores the definitions of communications interfaces and protocols. Compares those definitions with Matter and presents the possibility that Matter is not a protocol but […]
Teardown: Why the Kinect V2 doesn’t show “ghosts” that aren’t there
Do you believe in ghosts? And do you believe video gaming equipment can find ghosts lurking in your house? That’s the premise of some YouTube videos that use the Xbox Kinect gaming system to display what they have claimed are ghostly apparitions. That premise has been thoroughly debunked by several YouTubers, perhaps most notably Ken […]
What are the most common digital security techniques for storage systems?
By Rebecca Reinkunz, Release Manager, Hyperstone NAND flash memory is used in various consumer and industrial products, from laptops and mobile phones to industrial robotics, medical equipment, and embedded IoT devices, such as sensors and controllers. In our increasingly connected world, adequate and robust security measures are required at all vulnerable points in these applications, […]
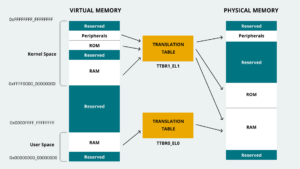
How many internal memories does an MCU have?
The number of internal memories in an MCU depends on how the memory is categorized. At the highest level, there are two; random access memory (RAM) and read-only memory (ROM). But, if the interest is in memory performance, there are different types of RAM and ROM. And these different types of memory can be employed […]
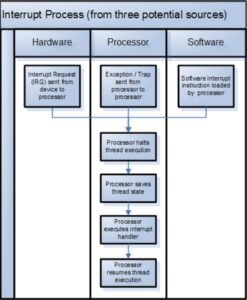
Exceptions, traps and interrupts, what’s the difference?
Exceptions and interrupts pause a program in response to an unexpected event in hardware or software. Interrupts are asynchronous events, and exceptions are synchronous events, but the difference between interrupts and exceptions also depends on the circumstances. For example, the definitions differ between x86 machines and ARM processors and between CISC and RISC processors. This […]