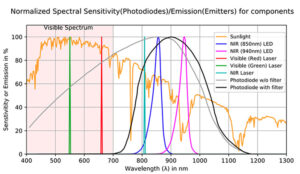
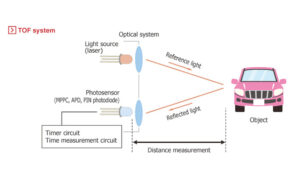
LiDAR systems and ToF techniques are critical to providing self-driving cars with a detailed picture of the surrounding and is used in many research applications as well. This is part three of a four-part series on LiDAR systems and ToF techniques. At the front end of a LiDAR system is the photon emitter and its […]
FAQ
LiDAR and Time of Flight, Part 2: Operation
LiDAR systems and ToF techniques are critical to providing self-driving cars with a detailed picture of the surrounding and is used in many research applications as well. This is part two of a four-part series on LiDAR systems and ToF techniques. Just as for radar and sonar, the LiDAR concept is simple but the execution […]
LiDAR and Time of Flight, Part 1: Introduction
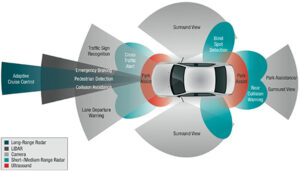
LiDAR systems and ToF techniques are critical to providing self-driving cars with a detailed picture of the surrounding and is used in many research applications as well. Many of the major automobile vendors, along with well-known non-auto companies such as Google, are devoting major resources to developing autonomous vehicles (often called “self-driving cars”). These vehicles […]
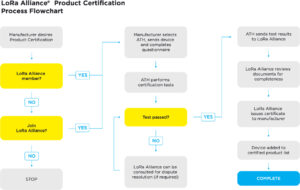
What is the LoRaWAN certification process?
The Internet of Things (IoT) is on the upward trajectory and seeing applications in an increasing number of sectors or industries. In these IoT applications, the IoT devices will be installed in remote or hard-to-reach locations and expected to operate for a long time without repair. Because the IoT devices collect and integrate many different […]
The fundamentals of MCU-based hardware virtualization
Virtualization, a powerful technology concept commonly associated with high-end applications in servers, is coming to the microcontrollers featuring multiple execution domains via multiple CPUs with a lock-step mechanism. The microcontrollers that incorporate hardware-based virtualization-assisted functions mark a new integration milestone in the embedded design world. Moreover, by running multiple software components on a single MCU […]
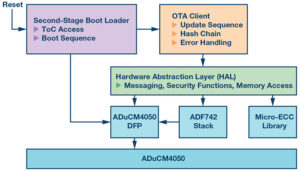
What matters for MCUs serving OTA functions in automotive designs
The technology features like over-the-air (OTA) software updates and data management are reinventing the hardware of today for the software of tomorrow. And if there is a single most prominent component at this technology crossroads, it’s the microcontroller. Moreover, the growing popularity of OTA functions is most visible in automotive environments where they wirelessly and […]
Teardown: Induction crystal ball gyrocopter toy
A little toy made in China called the Induction crystal ball uses a pair of coaxial rotors to rise in the air, helicopter-like. It powers the rotors enough to rise for a few seconds, then cuts the power back to gently float down until a proximity sensor in the base of the plastic body comes […]
What you need to know about MCUs for servo control
A servo motor, used for position feedback of angular rotation, applies pulse width modulation (PWM) signals for precise control over motion. Industrial design engineers can change the rotation angle and direction of the motor by varying the width of the PWM signal, and here, the role of MCU, which generates the PWM signal, inevitably becomes […]
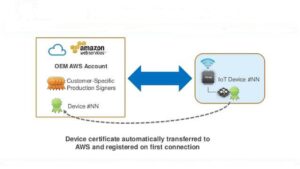
How zero-touch provisioning simplifies IoT links to cloud
Zero-touch provisioning eliminates the manual labor needed to connect devices to a network and allows these devices to be provisioned and configured automatically. It’s especially critical for small and mid-size companies in terms of cost and time of managing the provisioning logistics. While it’s a common concept in the networking industry at large, MCU suppliers […]
How the IIoT makes factories smart
Factories have always set their sights on increased productivity and cost reduction and the Industrial Internet-of-Things (IIoT) has impacted modern factories in a big way. To achieve those goals, modern factories have made automation and preventive maintenance using robotics, artificial intelligence (AI), and edge computing top priorities. In the next 10 years, factories with IIoT […]